For more phishing samples, see my phishy email collection.
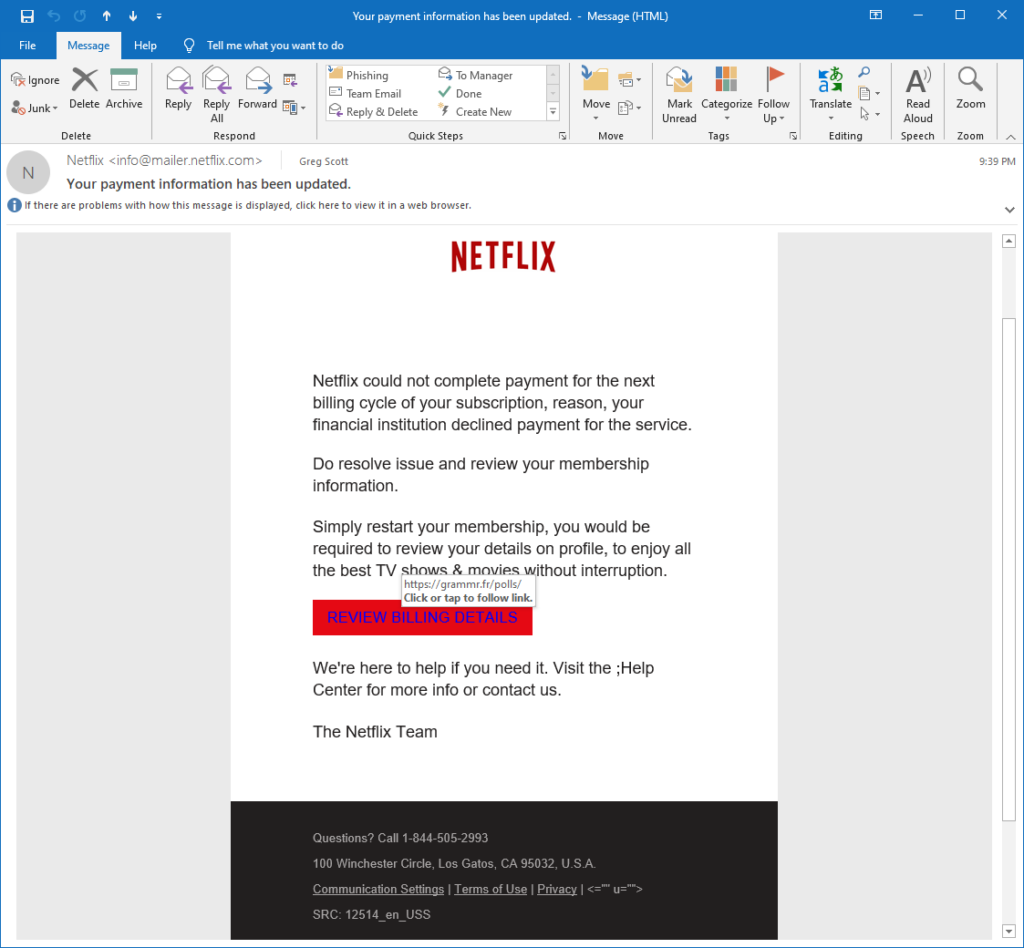
Somebody paid attention to details with this forgery. It only one small typo. There's no easy way to tell where this really came from by looking at the content. But hover over the link to see where it really points - why would Netflix have a billing center in France? I give it a B+. I'll paste in the relevant portions of the email header below the screenshot.
Relevant portion of the email header
.
.
.
Received: from mailer.netflix.com (50.242.102.125) by
mail2016.infrasupport.local (10.10.10.14) with Microsoft SMTP Server id
15.1.1531.3 via Frontend Transport; Mon, 26 Oct 2020 21:38:46 -0500
From: Netflix info@mailer.netflix.com
To: gregscott@infrasupportetc.com
Subject: Your payment information has been updated.
Date: Tue, 27 Oct 2020 02:38:45 +0000
.
.
.
Great job of managing details. Notice the forged Netflix name in the email header. But a whois lookup for IP Address 50.242.102.125 shows it actually came from Comcast.
NetRange: 50.128.0.0 - 50.255.255.255 CIDR: 50.128.0.0/9 NetName: CCCH3-4 NetHandle: NET-50-128-0-0-1 Parent: NET50 (NET-50-0-0-0-0) NetType: Direct Allocation OriginAS: AS7922 Organization: Comcast Cable Communications, LLC (CCCS) RegDate: 2010-10-21 Updated: 2016-08-31 Ref: https://rdap.arin.net/registry/ip/50.128.0.0
We can narrow it further by looking at the reverse DNS name. The Linux host command shows it's apparently part of a static IP Address block inside Comcast, which suggests it came from a compromised server and not a home computer.
# host 50.242.102.125
125.102.242.50.in-addr.arpa domain name pointer 50-242-102-125-static.hfc.comcastbusiness.net.

Recent Comments