The ransomware attack numbers are shocking. Here are a few ugly statistics, pasted from this source. This stuff is easy to find - just search for "ransomware statistics" and prepare for a shock.
- Ransomware costs businesses more than $75 billion per year. (Source: Datto)
- The average cost of a ransomware attack on businesses was $133,000. (Source: Sophos)
- 75% of companies infected with ransomware were running up-to-date endpoint protection. (Source: Sophos)
- A new organization will fall victim to ransomware every 14 seconds in 2019, and every 11 seconds by 2021. (Source: Cyber Security Ventures)
- 1.5 million new phishing sites are created every month. (Source: webroot.com)
- Ransomware attacks have increased over 97 percent in the past two years. (Source: Phishme)
- A total of 850.97 million ransomware infections were detected by the institute in 2018.
- 34% of businesses hit with malware took a week or more to regain access to their data. (Source: Kaspersky)
Do I really need to define a ransomware attack? A ransomware attack is when an attacker finds a way to scramble a victim's files and offers to unscramble them for a "small fee." It's a 21st century equivalent of an old-fashioned shakedown. Unfortunately, once the leaders of victim organizations get over their shock and denial, they're faced with two choices. Either pay the ransom or lose everything and rebuild it all from scratch. And most organizations are not prepared to rebuild everything from scratch.
And so, given the breadth and depth of the problem, what are we doing about it?
TV News shows such as 60 Minutes run wimpy stories that don't offer any solutions. Victimized entities try to persuade us they have everything under control. So, mostly nothing.
Great, what should we do?
We all know we're not supposed to click on email attachments. Unfortunately, too many of us still do. Given a company with 1000 employees, it's not rocket-science to figure out, the odds of somebody making a mistake are 1000 times greater than any one person making a mistake. More bluntly, no matter how much training we deliver to end-users, the odds are good somebody somewhere will do something stupid.
Sooner or later, malicious software will get inside. Here are a few tips to limit the damage.
- Make the principle of least privilege your friend. It means, give people only the privileges they need to do their jobs. It may limit the damage if somebody opens a malicious attachment.
- Use least privilege with programs, too. Only give programs enough privilege to perform their intended function. For example, why does a program that does, say, accounting, need write access into the company's authentication and authorization directory?
- Put a layer between all systems and their backups. If the systems don't know how to find their backups, then malicious software inside those systems won't know how to find and scramble their backups.
- Build a disaster recovery plan, practice executing it, refine the plan, and rinse and repeat. Do this on an ongoing basis. Plans that sit on a shelf quickly become obsolete and worthless. And get it through your thick heads that a successful ransomware attack represents a disaster, just like a fire or flood. Don't believe me? Just ask the growing number of victims.
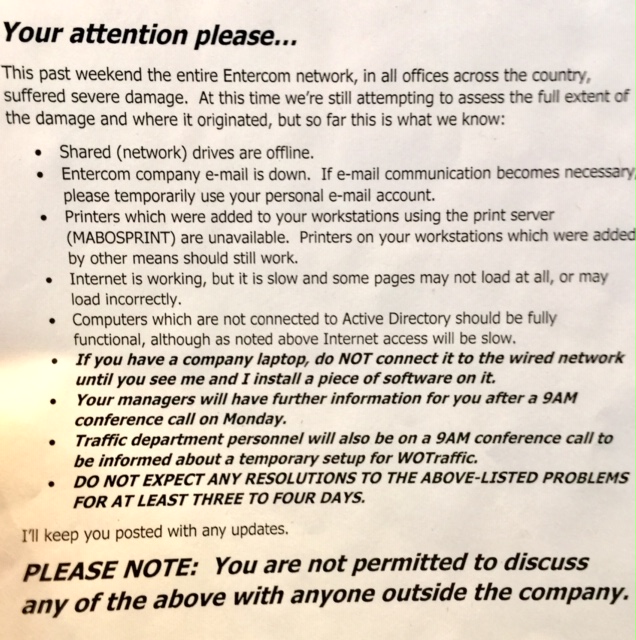
Beyond the statistics, here is one anecdotal story. A company named Entercom owns 250 radio stations across the United States, including all of CBS Radio and WCCO AM, the Minneapolis/St. Paul CBS Radio affiliate. Over the weekend of Sept. 7, 2019, somebody attacked Entercom and apparently shut down all its servers. Entercom is not talking, but news accounts like this one and this one offer clues.
Entercom is exhibit A about poor preparation and response. But first, my sympathies to the unsung heroes on the Entercom IT team, no doubt working 24x7 to recover. I've been on teams like that. They're not fun. It's a shame Entercom's management does not have their backs and the silence from Entercom's management only fuels speculation. And there are lots of questions. One big question - how did a malicious piece of software get so deep inside Entercom that it took down everything?
And that leads to what might be the number one biggie to fight back against this scourge. Bad guys spend all day probing good guys for weaknesses, and all night collaborating with other bad guys to improve the next day's probes. Good guys isolate themselves behind legal departments and politicians and cower in the dark. No wonder the bad guys are winning.
If the good guys want to win, level the playing field. Come out of the shadows and adopt open. Here is a presentation about why adopting open makes lots more sense than what we're doing now. And if my presentation is not persuasive, then just look at the ugly statistics again. How is the way we're handling it today working out? What was that definition of insanity again?
I would love to see a post-mortem on this after the dust settles, but given Entercom's silence to date, Entercom's managers will probably sweep the whole thing under the rug and try to pretend it never happened. And this is a media company that owns more than 250 radio stations. Shame on you, Entercom. You guys should know better.
Entercom, here is your opportunity to pull your management's heads out of a dark place and lead. Come clean with what happened. Share details in conferences. Broadcast it across your radio stations. As my fictional Fraud Analyst from Uncle Sam Bank, Jesse Jonsen would say, turn this lemon into a batch of lemonade and use this mess as an opportunity to educate the public. Who knows, it might even generate enough ad revenue to fund your recovery costs.

Trackbacks/Pingbacks